

Israel isn’t knee deep in an information war against the US and Europe
You’re right, they’re trying to spread their pro-genocide propaganda all over the world
Mastodon: @Andromxda@infosec.exchange
wiki-user: Andromxda


Israel isn’t knee deep in an information war against the US and Europe
You’re right, they’re trying to spread their pro-genocide propaganda all over the world


This issue is mainly just about votes, since these take up lots of storage space. The total amount of upvotes/downvotes would still be saved, but the individual votes of each user would get purged from the DB. Even though it mentions disabling comments once a post gets archived, I think this will be a separate option, that can be disabled by instance admins. If you still oppose this, you should comment on the GitHub issue, that’s where the devs are, not here.


Will you reconsider your decision once this gets implemented? https://github.com/LemmyNet/lemmy/issues/5016
It should save lots of storage space that would otherwise be used to store all the old votes from all the communities


Fixed that for you


Hands down, Rust 🦀


I believe Veyon can do this. Chris Titus Tech once made a pretty good video about it: https://www.youtube.com/watch?v=ysOr91dUy-8


Pirate party >>>>>>


Maybe bring back Tesseract? Why was it shut down in the first place?
Another idea I had: Hosting our own Matrix instance? That way, every community could create their own spaces while being independent from matrix.org and not putting more stress on their already overloaded servers. Running a modern Matrix server implementation like Conduit, which is written in Rust, shouldn’t require as much resources.


May I ask about the reason behind this?


Perhaps enable https://lemmy-federate.com ?


Probably the walls. Without them, the ceiling would collapse and everything in the room would be useless.


Not today, but recently at work, I, a DevOps engineer specializing in Linux and other Unix/Unix-like systems, was given the task of doing some admin and maintenance work on a few Windows servers…
I FUCKING HATE WINDOWS
THIS OS MAKES NO SENSE AND ADMINISTERING IT IS A NIGHTMARE
FUCK MICROSOFT!
You clearly forgot Hannah Montana Linux and Moebuntu


Yes, @oranki@lemmy.world wrote a great article about that: https://oranki.net/posts/2024-07-10-passkeys-on-grapheneos/


Yeah why would anyone pay 700 bucks for a highly restricted device, that can’t even play games online without an additional subscription. Just get a Steam Deck, which costs less, is portable, doesn’t require subscriptions, and basically works like a full PC.


Elon is probably proud of it.


Fuck yeah


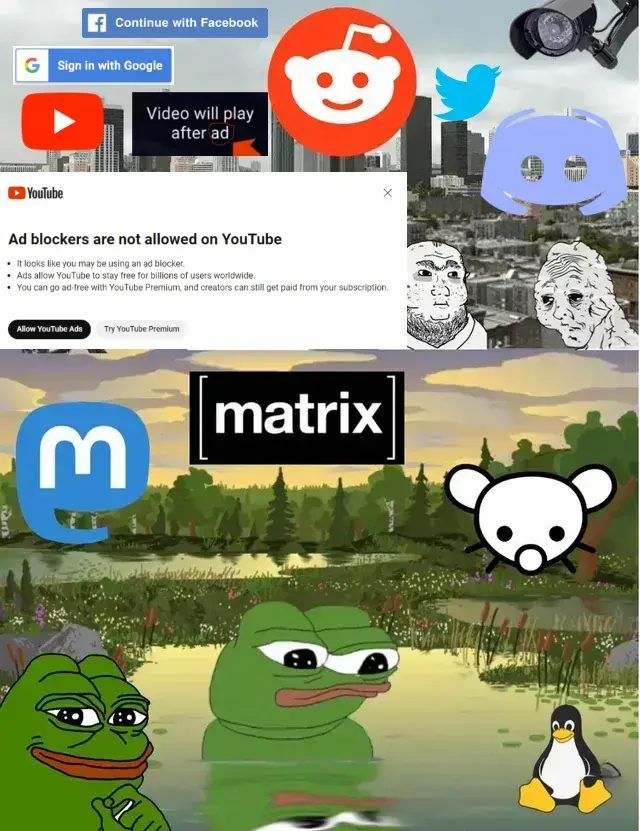
You mean like this?

Peppermint - not Ubuntu, but Debian, so it’s pretty similar